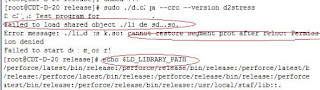
Failed to load shared object. cannot restore sgment prot after reloc permission denied
Initially I thought that this problem over my binaries are coming due to Permission errors. I checked the permissions on directories, binaries, executables. But all were fine. Then I though of running using 'su' or 'sudo' command, but to no avail.I searched through Internet and found that someone has got a similar error in CentOS too. It so happens that CentOS 5 has the SE Linux feature set to enforcing. So, sometimes when you install CUBRID on CentOS and try to start the cubrid services cubrid service start, you may encounter the following error:
[cubrid@localhost ~]$ cubrid service start
cubrid: error while loading shared libraries: /opt/cubrid/lib/libcubridsa.so.8: cannot restore segment prot after reloc: Permission denied
This error is not limited to installation. It can come while running an application too. It should be remembered that This problem is seen in Linux gcc 4.1.2 i686 i386 GNU/Linux flavors too. Resolution is same. While installation of any package or Starting any service on a RHEL or CentOS based Server you may receive following Error
cannot restore segment prot after reloc: Permission denied
This Error comes when SELinux setting is enabled on the server. Someone even reported this coming from java librarie. The error was while trying to run several programs. For example:
Exception in thread "main" java.lang.UnsatisfiedLinkError: /usr/lib/libjpcap.so: /usr/lib/libjpcap.so: cannot restore segment prot after reloc: Permission denied
How to solve Failed to load shared object Sgment Prot after reloc:Permission Denied Problem in Linux
No problems!!As already told you this comes due to Security-Enhanced Linux (SELinux). It is a Linux feature that provides a mechanism for supporting access control security policies through the use of Linux Security Modules (LSM) in the Linux kernel.
By Default SELinux is set to “enforcing” in CentOS on boot, this can be disabled permanently. To disable it edit file “/etc/selinux/config” and change SELINUX
To temporarily disable enforcement on a running system, type
/usr/sbin/setenforce 0
To permanently disable enforcement during a system startup
change "enforcing" to "disabled" in ''/etc/selinux/config''
It was a great relief to me when I got my control back on my binaries. Cheers!!
Tablet PC, the name itself propose that it's smaller in size compare to a desktop PC and significantly more compact than a laptop PC and are worked in various sizes (inches) from 5" to 10", yet the normal size is 7" of 8" (inches). document fill out
ReplyDelete